Although the cybersecurity landscape is repeatedly birthing improved and much more sturdy means of ensuring info protection, MD5 stays, as equally a tale of growth and among warning.Despite these shortcomings, MD5 continues to become utilized in various applications offered its efficiency and ease of implementation. When analyzing the hash values c
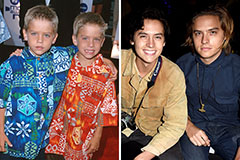 Dylan and Cole Sprouse Then & Now!
Dylan and Cole Sprouse Then & Now! Charlie Korsmo Then & Now!
Charlie Korsmo Then & Now! Erik von Detten Then & Now!
Erik von Detten Then & Now! Michelle Trachtenberg Then & Now!
Michelle Trachtenberg Then & Now! Brooke Shields Then & Now!
Brooke Shields Then & Now!